Figures & data
Table 1. SME categories according to their roles in the digital ecosystem.Citation27.
Figure 1. The research process.Citation42
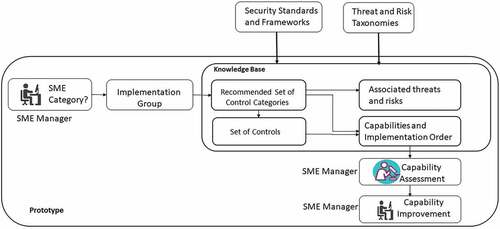
Figure 2. The meta-model of the Adaptable Security Maturity Assessment and Standardization (ASMAS) Framework.
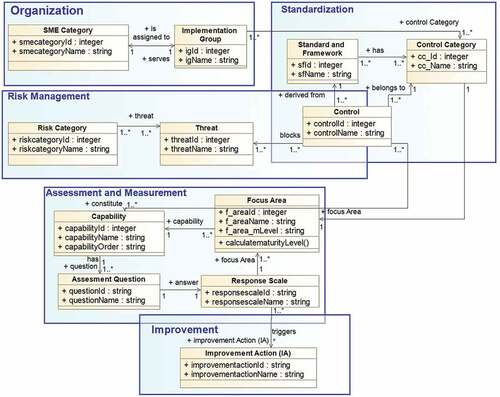
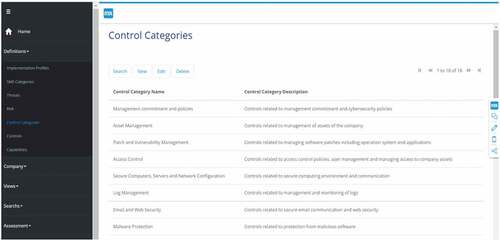
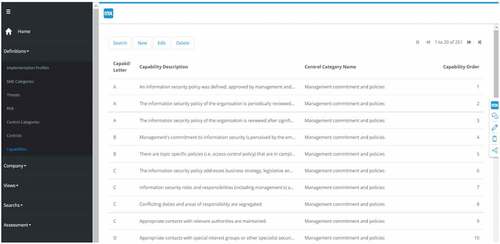
Figure 3. Control categories, implementation groups, and their associations with the SME categories.
Table 2. Mapping of the high-level requirements (HLRs) and the framework aspects.(O: Organizational, S: Standardization, RM: Risk Management, A&M: Assessment and Measurement, I: Improvement).
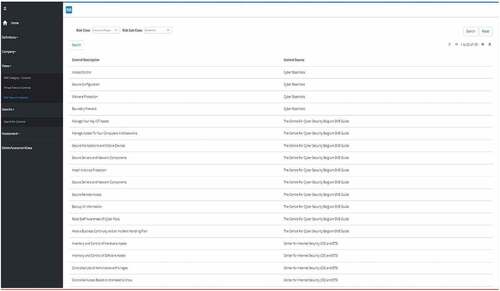
Table 3. The summary of control-related content of the knowledge base.
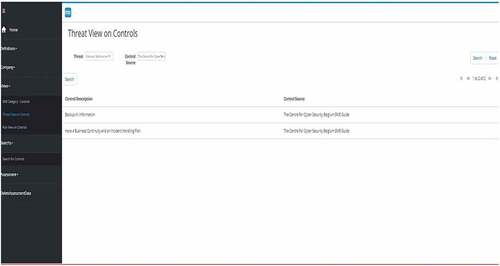
Table 4. The summary of capability, risk, and threat-related content of the knowledge base.
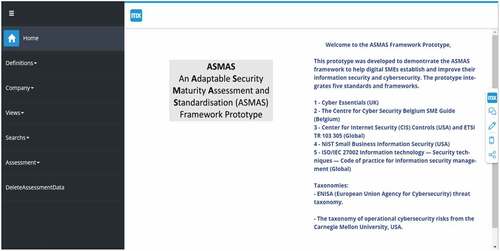
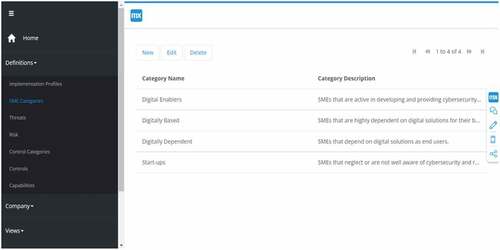
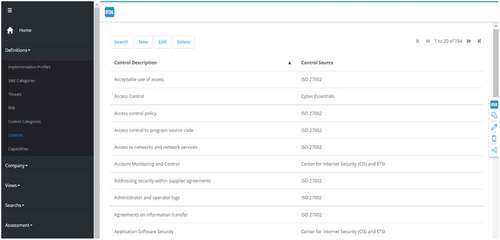
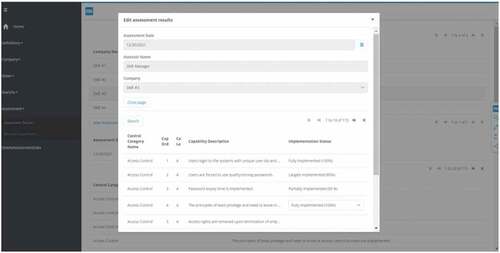
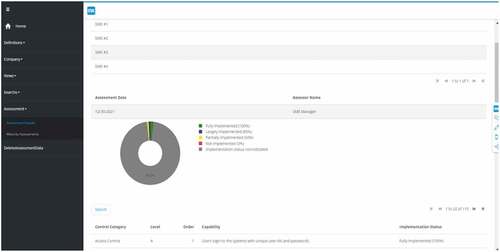
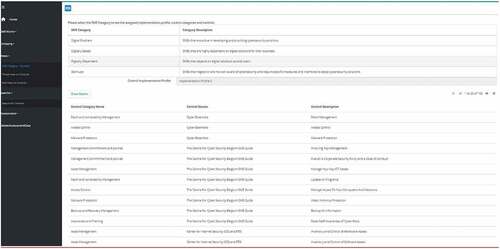
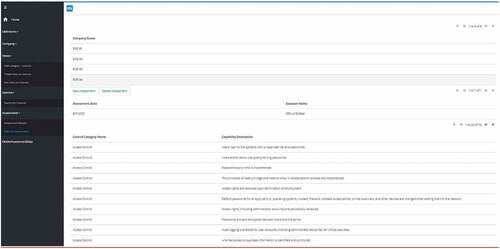
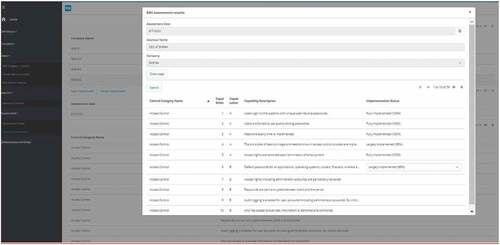
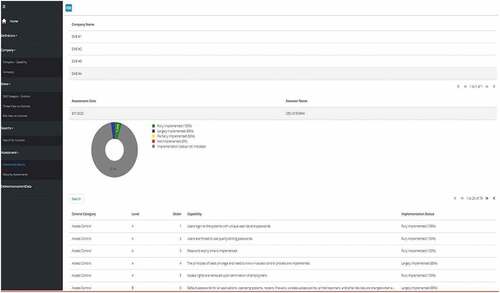
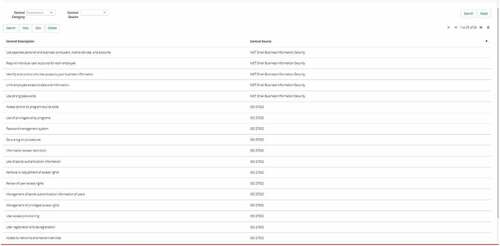
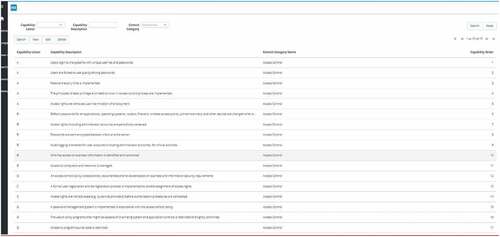
Table 5. The functions in the ASMAS framework prototype.
Table 6. Set of questions used to evaluate the utility of the ASMAS framework.
Table 7. Evaluation study participants’ characteristics
Table 8. Responses to the evaluation form statements.