Figures & data
Table 1. Network Security Situation Level Table.
Table 2. Acquisition data format.
Table 3. Types of Attacks and Corresponding Sample Numbers.
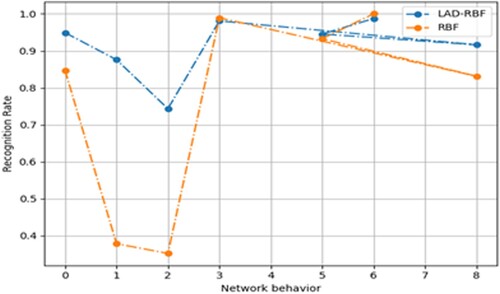
Table 4. Evaluation results for each method.
Table 5. Quantitative values of threat events.
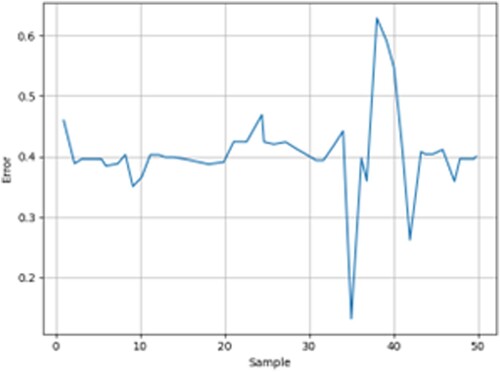
Table 6. Results of error evaluation indicators.
Table 7. Network Traffic Statistics under Normal Conditions.
Table 8. Packet statistics under normal.
Table 9. Time delay test results.
Table 10. Network traffic statistics under attack.
Table 11. Packet statistics under attack.
Table 12. Delay test results under attack.
Table 13. Sample Set.
Table 14. Comparison of methods.
Data availability
The experimental data used to support the findings of this study are available from the corresponding author upon request.