Figures & data
Table 1. Comparison of security properties.
Table 2. Proposed protocol communication overhead.
Table 3. Communication overhead of ,
and
ciphertexts.
Table 4. Experimental parameters.
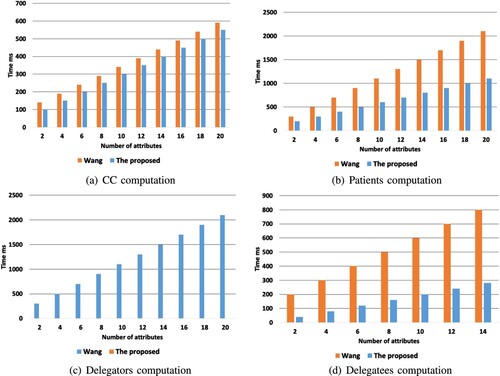
Figure 6. Computational cost comparison. (a) CC computation (b) patients computation (c) delegators computation and(d) delegatees computation.