Figures & data
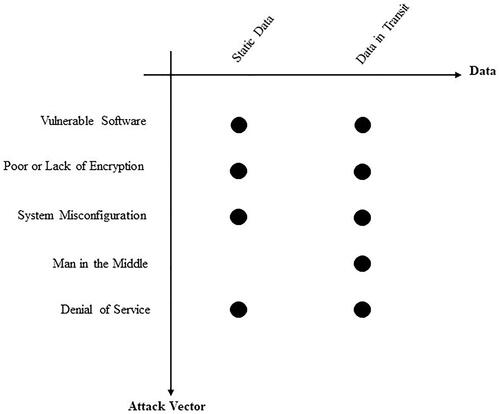
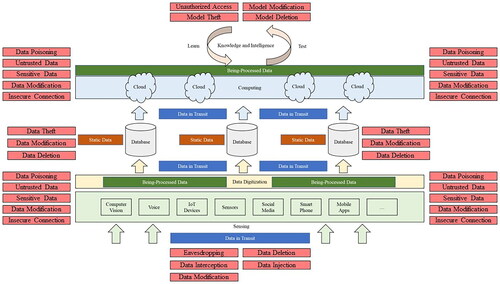
Table 1. Potential attacks on static data in intelligent systems.
Table 2. Potential attacks on data in transit of intelligent systems.
Table 3. Attack methods and attack types on data in intelligent systems.
Table 4. Attack methods on processes and components of intelligent systems.
Table 5. Attack methods on data and security characteristics.
Table 6. Attack methods on the processes and components and security characteristics.