Figures & data
Figure 1. Flow diagram for the dynamics of cybercrime depicting how people transition between compartments as individuals experience cybercrime.
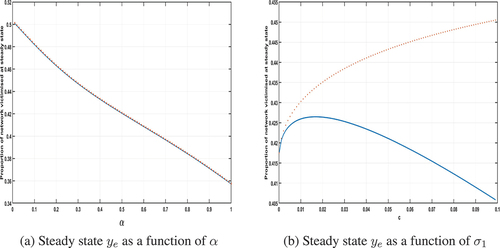
Figure 2. Plots of the steady-state proportion of the network that is victimised when the criminals are external to the network, i.e. with ψ = 0. Model parameters used: ,
,
,
, p = 0.75. In (a)
, in (b) α = 0.5.
Figure 3. Plots of the steady-state proportion of the network that is victimised when the criminals are internal to the network, i.e. with ψ = 1. The solid blue line is the value ye whilst the red crosses are given by which is the proportion of available population in the network that are victimised at steady state. Model parameters used:
,
,
,
, p = 0.75. In (a)
, in (b) α = 0.5.